Someone in the Intelligence community leaked online a secret catalog of cellphone spying devices used by law enforcement.
The Intercept has leaked online a secret catalog of cellphone spying devices, the precious document has been given to the online publication by someone inside the intelligence community.
The person who passed the document to The Intercept declared to be concerned about the growing militarization of domestic law enforcement.
"The Intercept obtained the catalogue from a source within the intelligence community concerned about the militarization of domestic law enforcement. (The original is here.)" states the post published on the Intercept.
"A few of the devices can house a "target list" of as many as 10,000 unique phone identifiers. Most can be used to geolocate people, but the documents indicate that some have more advanced capabilities, like eavesdropping on calls and spying on SMS messages. Two systems, apparently designed for use on captured phones, are touted as having the ability to extract media files, address books, and notes, and one can retrieve deleted text messages."
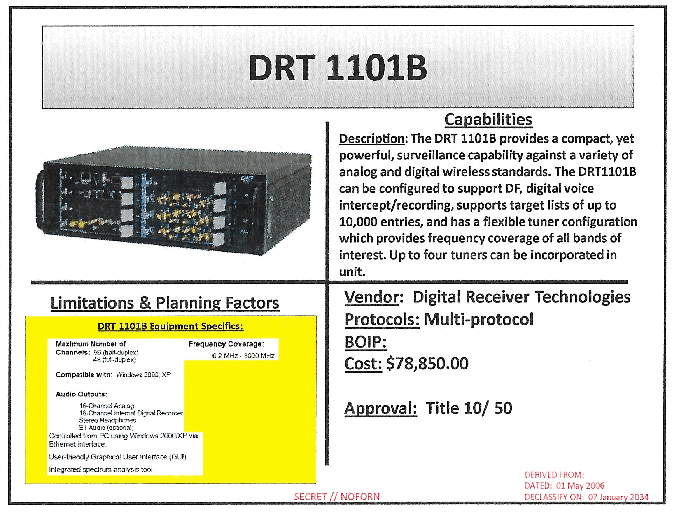
The catalog includes 53 cellphone spying devices, including Stingray I/II surveillance boxes and Boeing "dirt boxes."
There are some devices small enough to fit in a backpack such as the REBUS Ground Based Geo-Location that "provides limited capability to isolate targets utilizing Firewall option."
The document also includes many other cellphone spying devices that are less popular of the Stingray that could be used by law enforcement and intelligence agencies in various scenarios, including the deployment on drones and aircraft.
One of the spying devices is sold by the NSA, while another was designed for use by the CIA.
These systems are a long debated because they allow authorities to conduct dragnet surveillance, the cellphone spying devices have been used by local law enforcement agencies across the United States for a long time.
"The archetypical cell-site simulator, the Stingray, was trademarked by Harris Corp. in 2003 and initially used by the military, intelligence agencies, and federal law enforcement." continues the post. "Another company, Digital Receiver Technology, now owned by Boeing, developed dirt boxes — more powerful cell-site simulators — which gained favor among the NSA, CIA, and U.S. military as good tools for hunting down suspected terrorists. The devices can reportedly track more than 200 phones over a wider range than the Stingray."
The Intercept also reported the case of Marc Raimondi who was employed by the Harris company and that now is a Department of Justice spokesman who claim the agency's use of Stingray cellphone spying devices is legal.
Jennifer Lynch, a senior staff attorney at the Electronic Frontier Foundation has repeatedly expressed its disappointment at the use of these devices in a domestic context.
"We've seen a trend in the years since 9/11 to bring sophisticated surveillance technologies that were originally designed for military use—like Stingrays or drones or biometrics—back home to the United States," said Jennifer Lynch "But using these technologies for domestic law enforcement purposes raises a host of issues that are different from a military context."