The developers of the Dyre banking Trojan have released a new version of the malware that includes support for Windows 10 and Microsoft Edge.
The security firms Heimdal Security and F5 Networks have uncovered a new version of the Dyre (Dyreza) banking Trojan that includes support for Windows 10 and Microsoft Edge.
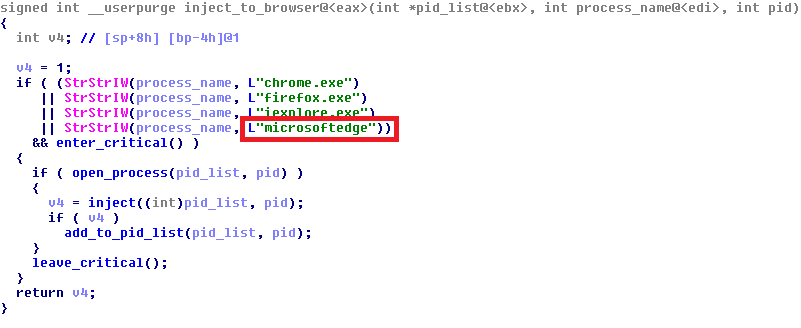
The new variant of Dyre now also targets Chrome, Firefox and Internet Explorer, and it is able to hook its code into the process of Microsoft Edge.
 According to the Heimdal Security more than 80.000 machines are already infected with Dyre Trojan across the world.
According to the Heimdal Security more than 80.000 machines are already infected with Dyre Trojan across the world.
The experts at F5 who analyzed the new Dyre Trojan have discovered that the authors have renamed some of the existing commands and have implemented new functionalities.
Below the list of new commands added to the new variant of the malware:
- 0xF1"lli" – Get the botid name
- srvv – Get the C&C IP
- dpsr – Get the data POST server IP
- grop – Get the botnet name
- seli – Get the self-IP
- gcrc – Get the fake pages configuration
- gcrp – Get the server-side webinjects configuration
- pngd – Get the account information stolen by the pony module
- sexe – Among other jobs, it copies the droppee path and its content both to Dyre's special structure and the configuration file on disk. It also tries to get the anti-antivirus module from the C&C.
- gsxe – Get the droppee path
The new commands are used to get the IP of the command and control (C&C) server, the botnet name, configuration for fake pages, configuration for server-side webinjects, account information stolen by the Pony module, and an anti-antivirus module.
The Dyte include a module specifically designed to locate security products installed on the infected machine and disable them, this module is named "aa32" on Windows 32-bit versions and "aa64" on 64-bit versions. The module is injected into the "spoolsv.exe" process and it is able to neutralize the principal antivirus software, including solutions designed by Avira, AVG, Malwarebytes, Fortinet, Trend Micro and also the Windows Defender service.
To make the malware more difficult to analyze, the authors of the last version have encrypted hardcoded debug strings and only decrypt them during runtime.
Previous versions of Dyre gain persistence by using a Run key in the registry, but the last one used a scheduled task that is run every minute.
"We conclude from the addition of these features that the authors of the malware strive to improve their resilience against anti-viruses, even at the cost of being more conspicuous," is reported in the blog post published by F5. "They also wish to keep the malware up-to-date with current OS releases in order to be 'compatible' with as many victims as possible. There is little doubt that the frequent updating will continue, as the wicked require very little rest."
Experts believe that the new variant of Dyre is spreading in the wild to monetize the coming holiday season.
"The timing of this new strain is just right: the season for Thanksgiving, Black Friday and Christmas shopping is ready to start, so financial malware will be set to collect a huge amount of financial data. Users will be busy, prone to multitasking and likely to choose convenience over safety online," Heimdal Security noted.