The popular expert and Shodan creator John Matherly found over 650 terabytes of MongoDB data exposed on the Internet by vulnerable databases.
Last week my old hosting provider GoDaddy created me a lot of problems so I had no opportunity to write about this interesting story, now I passed to a better provider and I decided to do it.
There are at least 35,000 vulnerable MongoDB databases exposed on the Internet, the data they contain is exposed to cyber attacks. It has been estimated that nearly 684.8 terabytes of data are at risk, and most disconcerting aspect of the story is that this data is growing day by day.
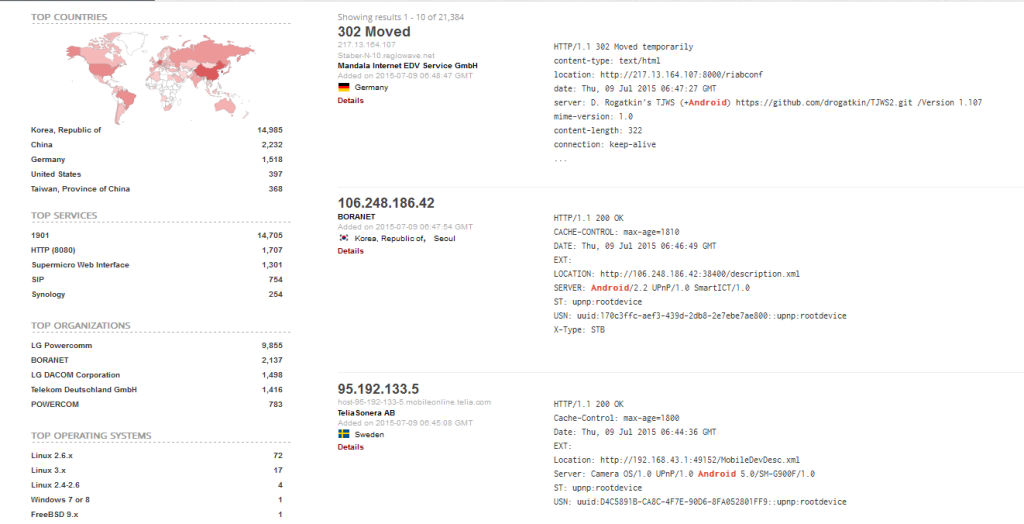
The estimates are the result of a scan performed over the past few days by John Matherly, the popular cyber security expert, and creator of the Shodan search engine for Internet-connected devices.
MongoDB is a popular alternative to SQL, open source, many companies already use it, including "The New York Times", "Ebay", and "Foursquare." John Matherly argues that around 30.000 databases are exposed because administrators are using old versions of MongoDB, and these old versions fail to bind to localhost
Matherly has already warned the IT industry about the presence of vulnerable MongoDB online, in July he revealed that many MongoDB administrators exposed something like 595.2 terabytes of data by adopting poor configurations, or un-patched versions of the MongoDB.
In July, he found nearly 30,000 unauthenticated MongoDB instances, then he decided to monitor the situation over the time.
Recently the security researcher Chris Vickery confirmed that information exposed in such databases was associated with 25 million user accounts from various apps and services, including 13 million users of the OS X optimization program MacKeeper. Vickery discovered that data records include names, email addresses, birth dates, postal addresses, private messages and insecure password hashes.
Matherly now discovered further 5,000 insecure instances since July, a somewhat surprising result giving that newer versions of the database no longer have a default insecure configuration.
"By default, newer versions of MongoDB only listen on localhost. The fact that MongoDB 3.0 is well-represented means that a lot of people are changing the default configuration of MongoDB to something less secure and aren't enabling any firewall to protect their database." Matherly wrote in a blog post Tuesday
"It could be that users are upgrading their instances but using their existing, insecure configuration files."
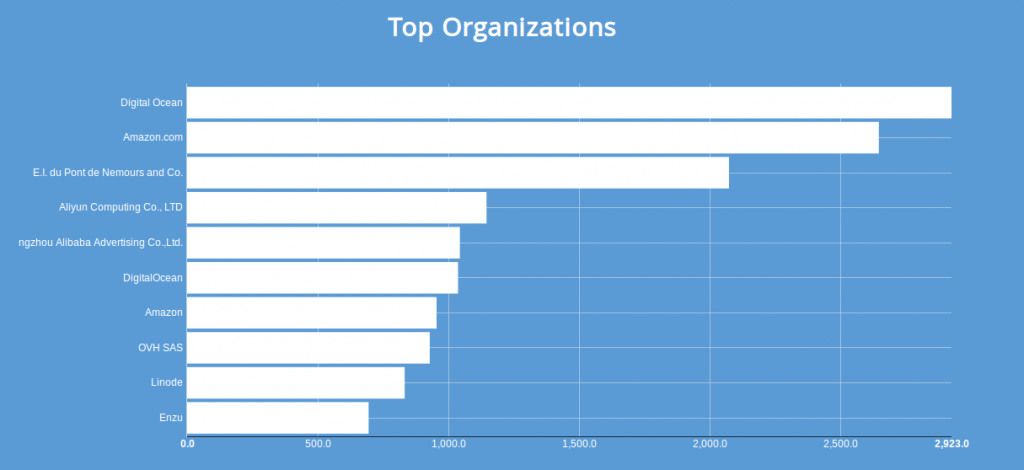
Matherly observed the majority of vulnerable databases are hosted on cloud computing platforms run by Amazon.com, Alibaba Group and DigitalOcean.
Unfortunately, many other vulnerable databases are exposed on the Internet including Redis, CouchDB, Cassandra and Riak as confirmed by Matherly.
"Finally, I can't stress enough that this problem is not unique to MongoDB:Redis, CouchDB, Cassandra and Riak are equally impacted by these sorts of misconfigurations." explained Matherly.


