Security experts at Palo Alto Networks have uncovered a new strain of malware dubbed BackStab that steals local mobile data backups.
Security experts at Palo Alto Networks have uncovered a new strain of malware dubbed BackStab that steals local mobile data backups and transfer it to the C&C server.
The malware is not able to steal data from the mobile device, instead it searches for data backup from the infected PCs. The malware scans for backups created by the mobile devices or by any other software that creates automatic backups.
BackStab Malware is able to Steal both iOS and BlackBerry Backups via compromised computers.
The malware exploits the fact that many backup tools don't implements encryption, so the malicious code easily finds the backups and access data it contains.
As explained by the experts, the BackStab malware doesn't need to have higher-level privileges or root access to the device or the infected computer.
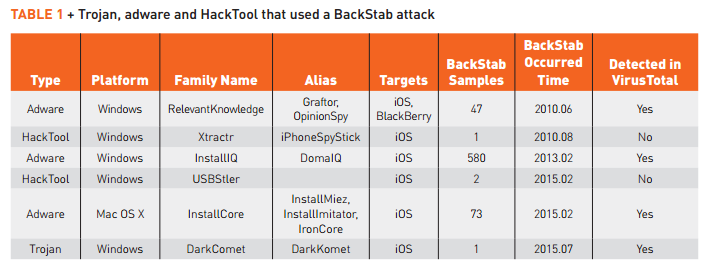
BackStab has been in the wild for over five years, the experts at Palo Alto Networks have discovered six trojan families that used the technique to steal backup data in attacks across 30 countries.
"We have identified 704 samples of six Trojan, adware and HackTool families for Windows or Mac OS X systems that used this technique to steal data from iOS and BlackBerry devices. These attacks have been in the wild for over five years, and we have observed them deployed in over 30 countries around the world." state a blog post published by PaloAlto Networks
According to Palo Alto researchers BackStab still not supports Android backups.
The experts provided a detailed description about how the BackStab works and mitigation strategies.
"Under certain conditions, mobile devices automatically create un-encrypted backup files on a local computer when they are attached through a USB port. Apple iOS devices began doing this when iTunes backup was introduced with the first generation iPhone in 2007. When users choose the default backup options, the contents of their phone is stored, unencrypted on their computers local hard drive in a well-known location. Forensics experts have known about this behavior for years and have exploited it to gain access to iOS device content even when they cannot directly access an iPhone due to it's strong protections."
Security experts suggest users to use a backup solution that implement data encryption, keep the OS and the application up to date, and "do not click "Trust" on the popup that appears every time they connect their phone to a new computer."
Enjoy the BackStab: Mobile Backup Data Under Attack from Malware report.


